Login with Okta
Okta support is limited to those organizations on the Codecov Enterprise plan or those organizations using Codecov's Dedicated Enterprise Cloud (DEC) offering. If you're looking to add Okta supported for your Enterprise plan (not DEC), please visit this page instead.
High level steps
- Create Okta application
- Share Okta client_id, client_secret, domain with Codecov team
On sharing Okta app credentialsPlease do not email or send unencrypted credentials. Please work with your Codecov representative or email [email protected] for one of several secure methods for sharing credentials.
A common method is to encrypt credentials using Codecov's Public PGP Key.
Create a custom app in Okta
This will need to be done by an Okta administrator for your org. The admin dashboard is typically available at https://<myorg>-admin.okta.com
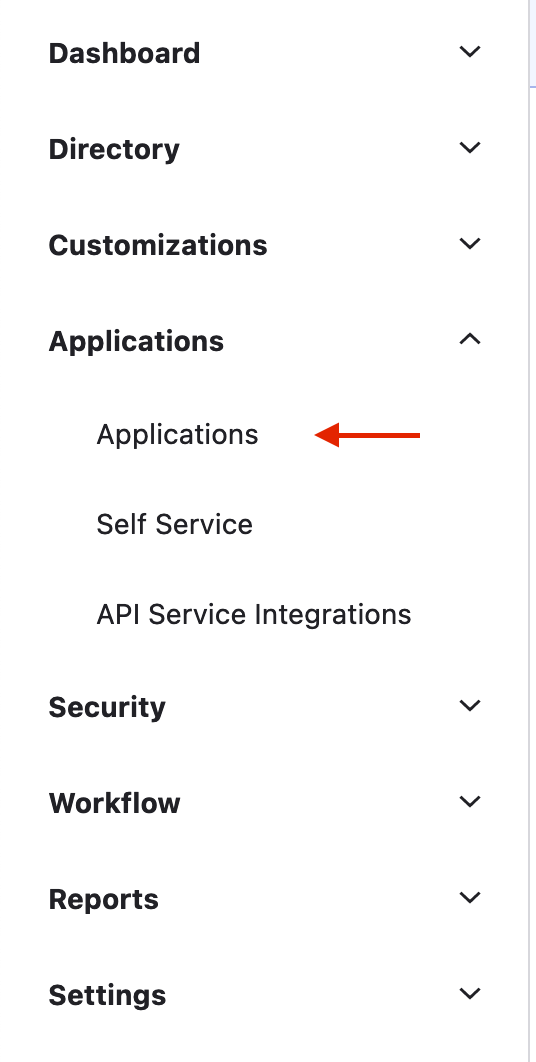
From the Okta administrator menu select “Applications > Applications”:
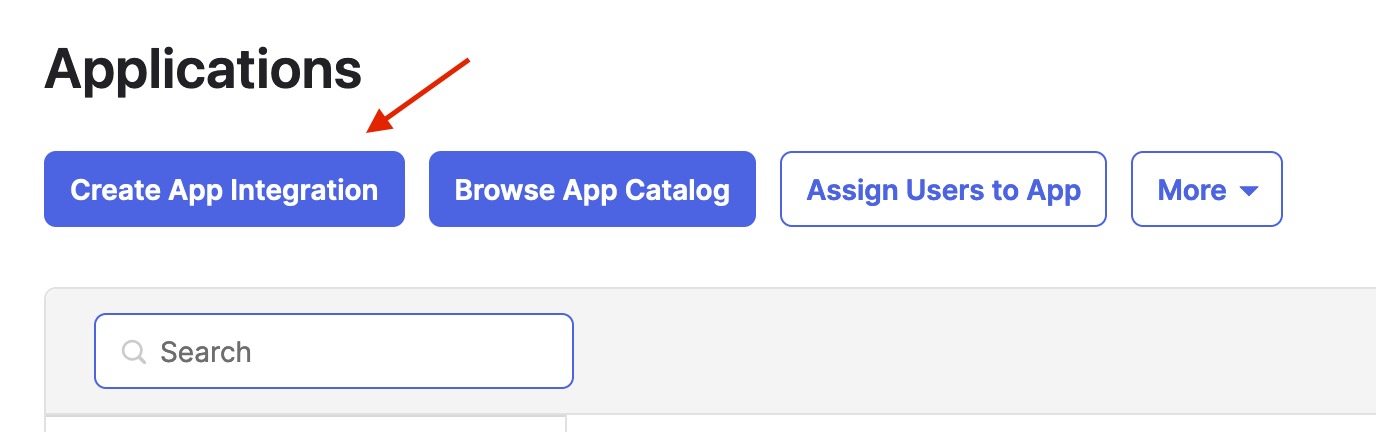
Click on “Create App Integration”:
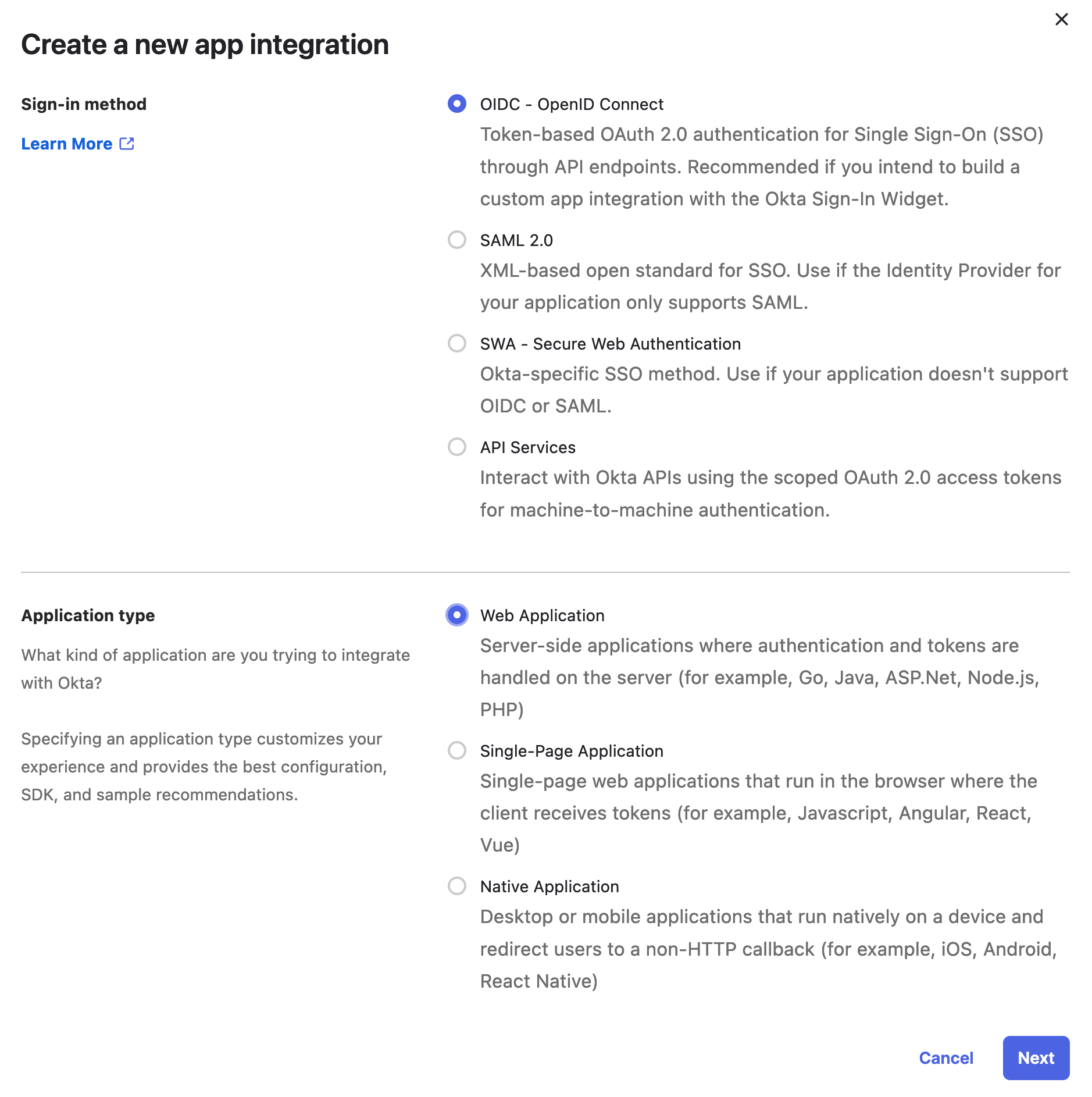
Select “OIDC - OpenID Connect” and “Web Application” and then press “Next”
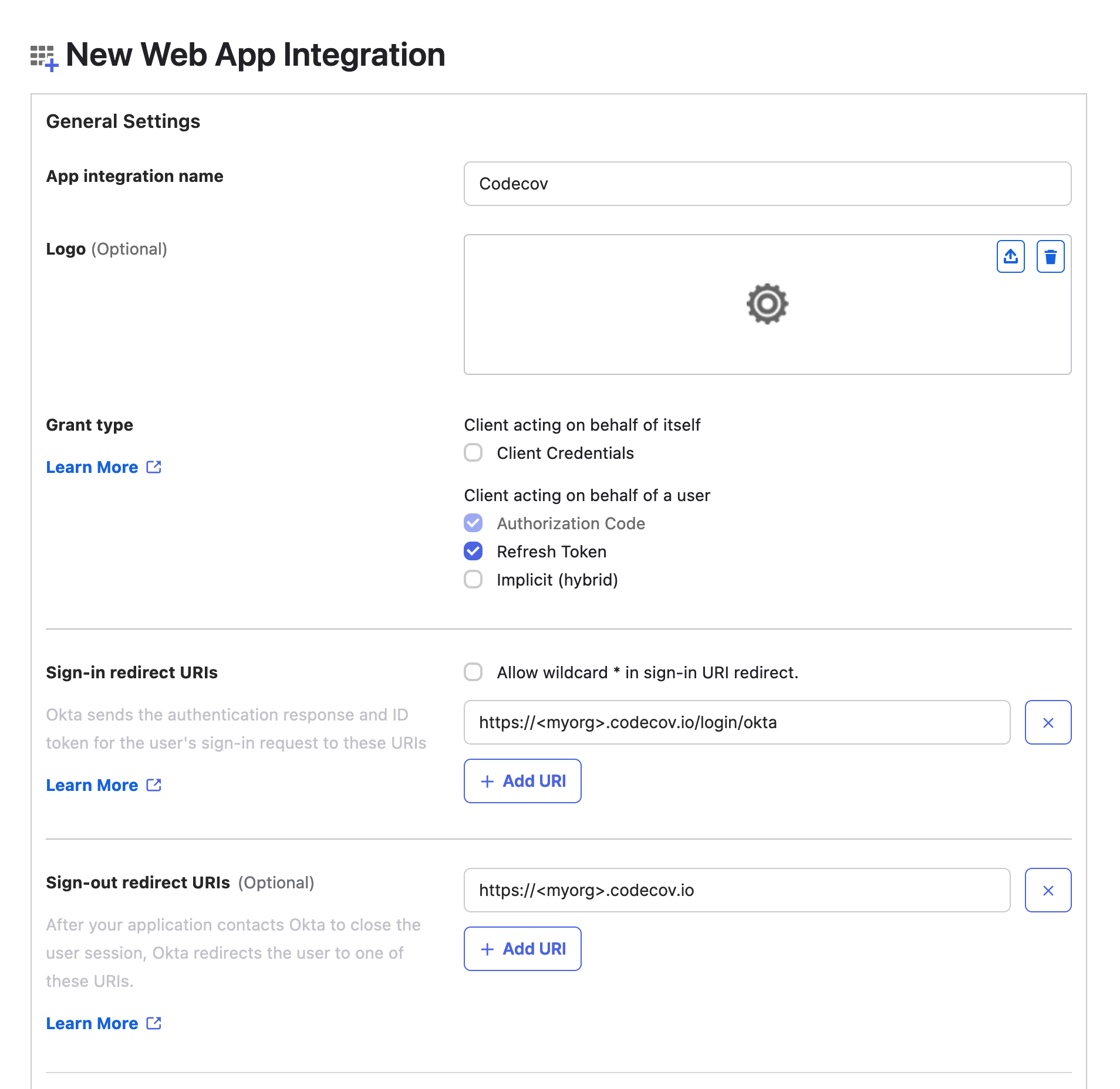
Fill out the app integration form:
- Give the app a name - this is what users signing in will see when granting access to Codecov
- Make sure “Authorization Code” and “Refresh Token” are selected under the “Grant type” section
- the “Sign-in redirect URI” needs to be very specific. It should be
https://<myorg>.codecov.io/login/okta(replacing<myorg>with the subdomain of your Codecov Dedicated Enterprise Cloud instance).
The “Assignments” at the bottom of the form are up to you. These settings allow anyone in your organization to access Codecov:
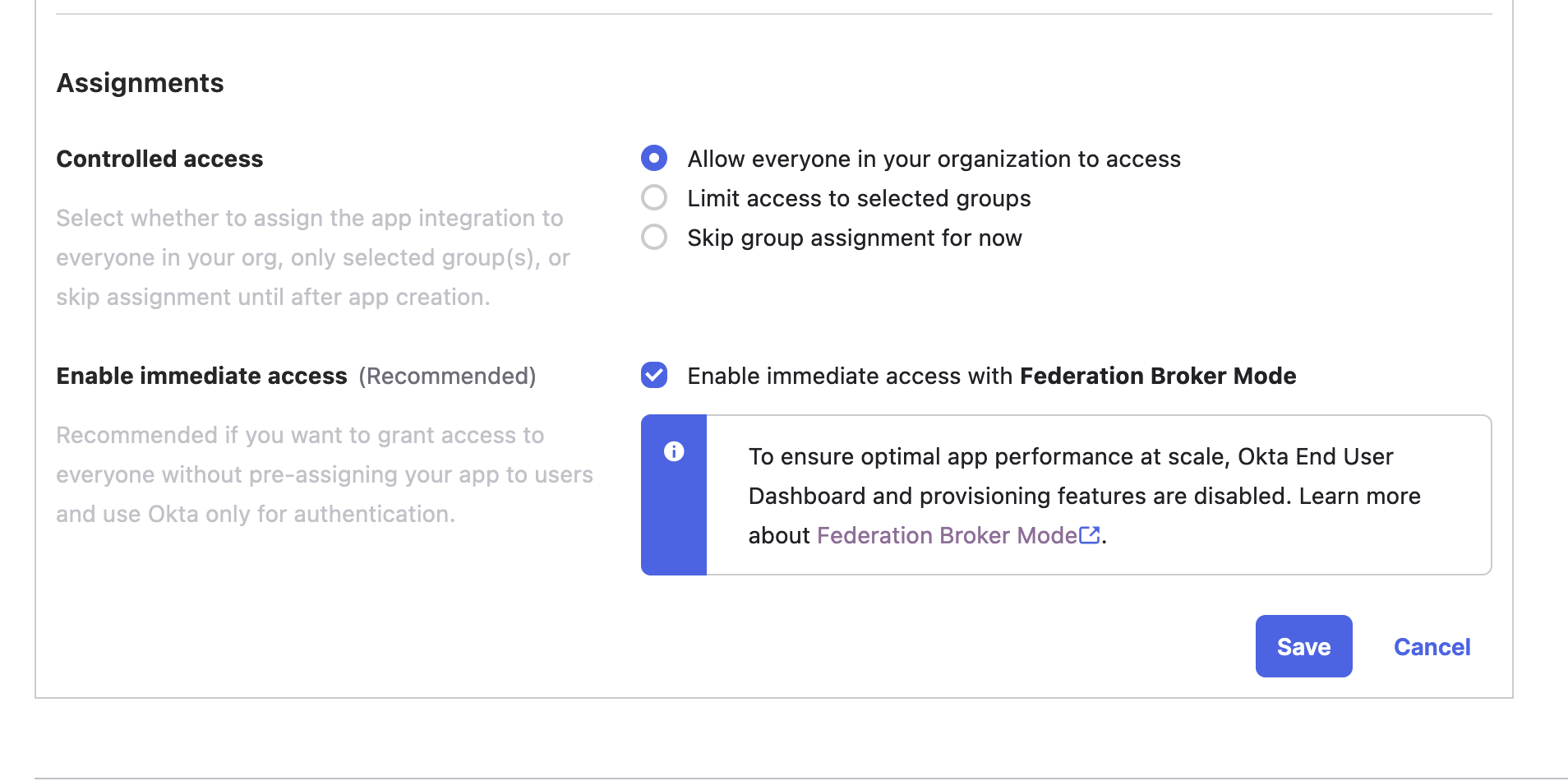
Click “Save” to create the application and then note the “Client ID” and “Client Secret” on the following screen:
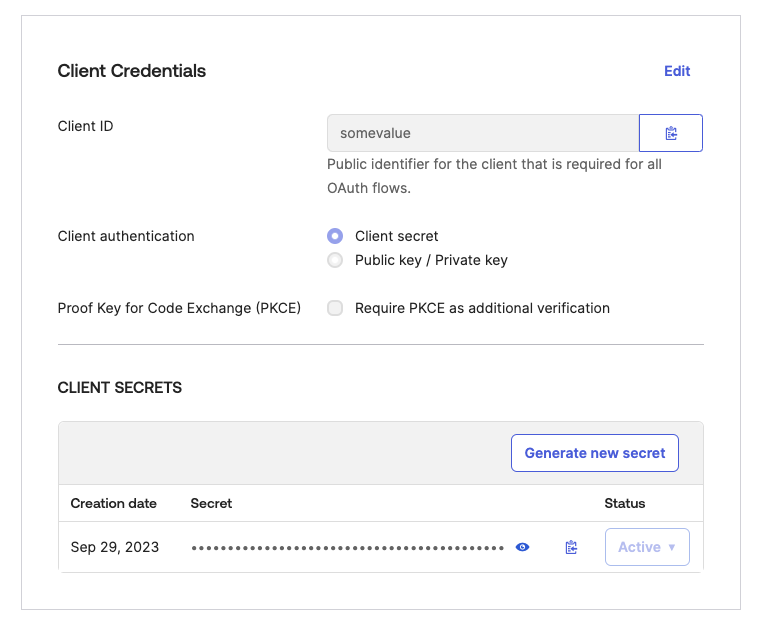
Provide these 2 values to the Codecov team (along with your Okta domain) and we’ll get your Dedicated Enterprise Cloud instance configured to login with this Okta application.
Codecov Login
After your Codecov Dedicated Enterprise Cloud instance and Okta app have been created, the view for login should look like below:
Login with Git codehost or Okta

Login exclusively with Okta
If you would prefer to exclusively allow logging in with Okta, please reach out to your account manager at Codecov.
If you are a self-hosted customer, you can make the following addition to your install YAML.
setup:
disable_git_based_login: trueLogin exclusively with Okta

Updated 6 months ago